About Lares
Lares® (Lar-Res) is a Denver, CO cybersecurity consulting company that prides itself on its ability to provide continuous defensive improvement through adversarial simulation and collaboration. Lares can help your organization validate its security posture through offensive security-focused services such as complex adversarial simulations, network penetration testing, application security assessments, insider threat assessments, vulnerability research, continuous security testing, virtual Chief Information Security Officer (CISO) services, and coaching.
Here at Lares, we want to help you make the most informed security decisions you can for your organization by giving you confidence. Confidence to defend against attackers with the tools at hand, address security and compliance concerns, and pass audits and assessments.
What is Purple Team?
For those that remember art class, what happens when you take some red paint and some blue paint and mix them together? You get purple.
It is commonplace for organizations that have built out an offensive (red) team and a defensive (blue) team to adopt the idea that the two will seamlessly collaborate, work together often and be very open to communication. Unfortunately, this is easier said than done and usually not in practice. No one can whistle a symphony.
The purpose of the purple team is to bridge this historical gap between these two teams in order to create the communication channels needed for success. It is critical to create an open dialogue to not only facilitate knowledge transfers and cross-training opportunities between these teams but also to aid in their maturity. You are investing in your people so why not get the best possible ROI.
If 60%, 80%, or all of your workforce has now gone full remote WFH, what does that mean for your security controls? How are they being re-evaluated for effectiveness during this transition? If initial access makes a shift to the home user, given they likely have remote connectivity right into the corporate network from home, does that then mean the corporate network initial access has now become lateral movement? Aggressors will (and some already are) make shifts to targeting the potentially softer target your users present while they WFH. Once they are compromised, even an unintentional compromise through some iffy software or pirated movies into the home network may lead an otherwise low-level threat to now have a direct line into the organization.
Security posture is never done. It is not a checkbox that will ever have the complete option ticked. Through purple team engagements, we put the spotlight on habits, trends, gaps, practices, and processes for both technical elements as well as human beings. One could almost argue it’s an investigation designed to elevate these questions high up and then go low-level into why they are what they are.
You must stay a moving target in a sense. Given the statements above regarding WFH and aggressor tactics, it is truly critical to have your capability to adapt tested. When the threat suddenly shifts tactics or decides to come back at you with an entirely new intrusion set, how do you prepare? You train. Just like anything else. It is paramount to keep “security fit”. The purple team workflow keeps your red and blue teams in the gym, in the dojo, practicing, training. To be prepared for the title fights to come as best as possible.
Purpose
By leveraging the existing skills and talents blue and red teams bring to the table and using them to identify strengths and weaknesses across the organization’s security controls, we can accurately measure those controls and the maturity of the organization’s progress.
Another core benefit is the creation of a think-tank mentality amongst all the participants which results in a creative and proactive approach to problem-solving. Leadership teams become far more informed when it comes to making data-driven decisions based on the information and lessons learned throughout each iteration of the purple team process.
Mitre ATT&CK and its Role
The MITRE ATT&CK framework is a knowledge base that provides details on attacks and remediation information about common tactics, techniques, and procedures (TTPs) leveraged by adversaries. ATT&CK has grouped and categorized them by their use in the cyber kill chain:
- Initial Access
- Execution
- Persistence
- Privilege Escalation
- Defensive Evasion
- Credential Access
- Discovery
- Lateral Movement
- Collection
- Command and Control
- Exfiltration
- Impact
Lares engineers are experts in the execution and understanding of these TTPs and we create test cases for each individual TTP found in ATT&CK as well as custom and more advanced variants to assess an organization’s coverage across a spectrum of intrusion sets and scenarios. These test cases are executed during purple team engagements in waves to measure the efficacy of the client’s security controls.
Advantages of ATT&CK
ATT&CK provides an excellent knowledge base that provides red and blue teams a centralized location to test their security controls, train internal teams in TTPs used by actual aggressors, enrich existing threat intelligence, and affords stakeholders the ability to make critical decisions based on data analytics.
Disadvantages of ATT&CK
Nothing is a silver bullet and ATT&CK is no different. The TTPs listed, while constantly being maintained and updated, is not something that should be viewed as ‘complete’. Lares recognizes that TTPs do not exist in a vacuum. While ATT&CK is an excellent tool to guide testing efforts and ensure coverage of commonly used TTPs, real-world attacks chain these techniques together to accomplish the desired endgame. Lares has taken a more robust approach. Therefore, the Lares team has developed a multi-tiered approach to Purple Teaming. The Lares Purple Teaming pipeline includes multiple phases that aim to measure the client’s security posture in an ‘all dimensions’ perspective. This results in an accurate depiction of the effectiveness of technical security controls, security-related processes, and defender skills.
Adversarial Collaboration Service Components
Collaborative security testing, at the end of the day, is about data analysis. How come X was not detected or how long did it take and why was it detected here but not there. We are hunting for answers and solutions. The process of adversarial collaboration is made up of many phase-based interactions. However, despite these being intentionally designed to flow from one to another in order, they do not have to be engaged in their entirety.
While the Initial Meetings and Interviews and Laying the Foundations descriptions below are always going to happen at the beginning of any engagement, the others can be isolated depending on an organization’s security program‘s achievements and the desire to either improve them further or confirm its efficacy from an unbiased service provider.
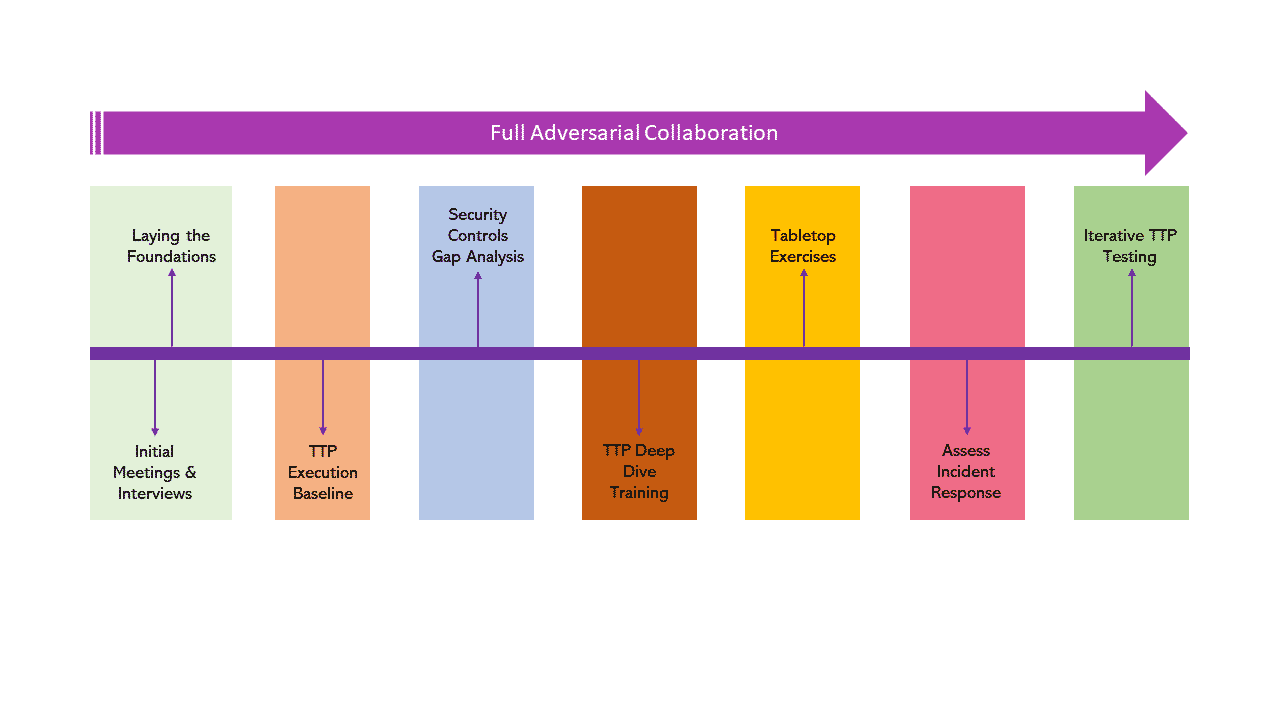
Initial Meetings and Interviews
- Carefully listening to your concerns and requirements
- Designing the outline and confines of the engagement
Laying the Foundations
- Creating the processes needed for engagement execution
- Establishing where your existing security controls fit across the kill chain
TTP Execution Baseline
- establish a baseline
- builds the realistic picture of the current state of security controls
Security Controls Gap Analysis
- leverage results from baseline
- provide insights into where strengths and weaknesses exist
TTP Deep Dive Training
- explore each attack in-depth
- blue and red teams gain valuable insights into how they work at a low level
Tabletop Exercises
- ‘shadowboxing’ through various attack scenarios
- collaboratively discuss campaigns and intrusion sets and how to approach defensive strategy
Assess Incident Response
- Take a close look at and evaluate IR process
- Identify skill gaps in the defenders to focus training for
Iterative TTP Testing
- Once is not enough. Iteration over previous TTP waves to confirm defensive progress state was reached
- Execute variations and more advanced tradecraft
Adversary Simulation
- Perform targeted and covert engagement against the organization
- Simulate advanced aggressors to test adaptive skills and lessons learned
Defensive Maturity Review
- Final analysis and review of all progress made throughout the entirety of the engagement
- Ensure defensive milestones and desired state is achieved
Red and Purple Team Differences
While the red team is executing security tests for the organization that directly assists the blue team through their findings, there are differences between red and purple team engagements:
- Purple team engagements integrate both blue and red teams into an interactive and collaborative union.
- Purple team engagements focus on coverage analysis between red and blue teams.
- Purple team engagements drive progression in real-time. Defensive and offensive maturity is being evaluated each step of the way
Are You Ready?
While purple team engagements do provide an extremely complete set of processes and evaluations, it is not always where you should begin. The purple team will assess how the existing security programs at an organization have been implemented so it is important to have these programs in place beforehand.
There are however steps and phases in a purple team that can help accomplish and verify positive progression in those security programs being built out along the way. Training, for example, can confirm red and blue team knowledge, skills, and execution capabilities while the underlying security program and practices are still being developed. Another example is the Lares Defensive Controls Analysis component which can be isolated and engaged with your organization to view how they are performing, where gaps may exist, which products are not functioning as advertised, and use this analysis to make highly informed decisions going forward.
The overall point is that security is not a static thing. It is ever moving and evolving. Because of this basic principle, an organization’s security programs must be continuously evaluated and tested at levels that will keep all parties involved on their toes. Everyone should be constantly learning, seeing their skills increase, maturing the organization as a whole, and understanding that we all need to work together in order to see change come to be.

