At the recent CUNA Technology Council and CUNA Operations and Member Experience Council Conferences in Chicago earlier this month, CUNA Chief Compliance Officer Jared Ihrig emphasized that cybersecurity is among the organization’s top examination priorities in 2019 and beyond. “Security, confidentiality, and integrity of member information remains a key supervisory priority for NCUA,” said Ihrig. NCUA will use the Automated Cybersecurity Assessment Tool (ACET) in their examinations of credit unions with $250 million and more in assets in 2019, and that will be expanded even further in coming years.
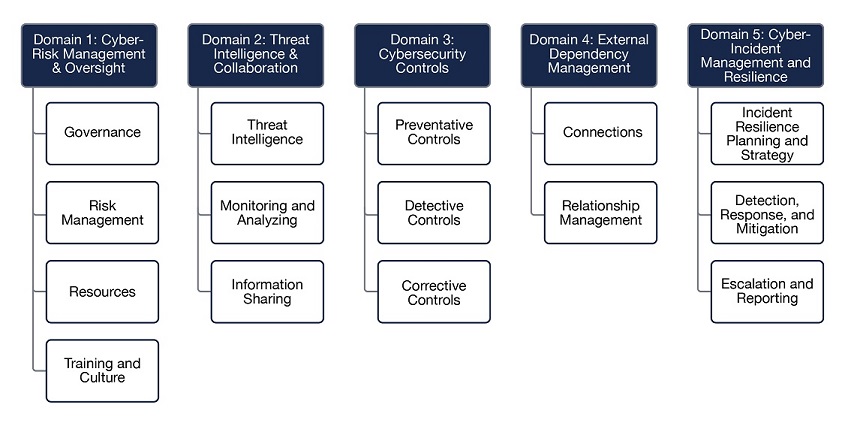
Though there are 5 cybersecurity domains defined, as depicted below, the majority of Credit Unions that we work with often skip the most important aspect of the ACET – the definition of the Inherent Risk Profile.
The Inherent Risk Profile identifies activities, services, and products organized by technologies and connection types, delivery channels, online/mobile products and technology services, organizational characteristics, and external threats. At first glance, it may appear to be an overwhelming task and you may think “OK, I’ll come back to this later after I implement the components of the Cybersecurity Maturity Domains.” Perhaps the best way to look at the Inherent Risk Profile is to compare the ACET to a recipe for baking a pie.
The Cybersecurity Maturity phase is essentially the ingredients for making your pie. Though these are necessary in order to create the pie, without knowing the ingredient measurements, you will have a very hard time turning the raw ingredients into something that is edible. This is where the Inherent Risk Profile phase comes into play. By identifying the risks for each category, your CU will be able to measure the amount of additional effort that is required to reduce your overall risk.
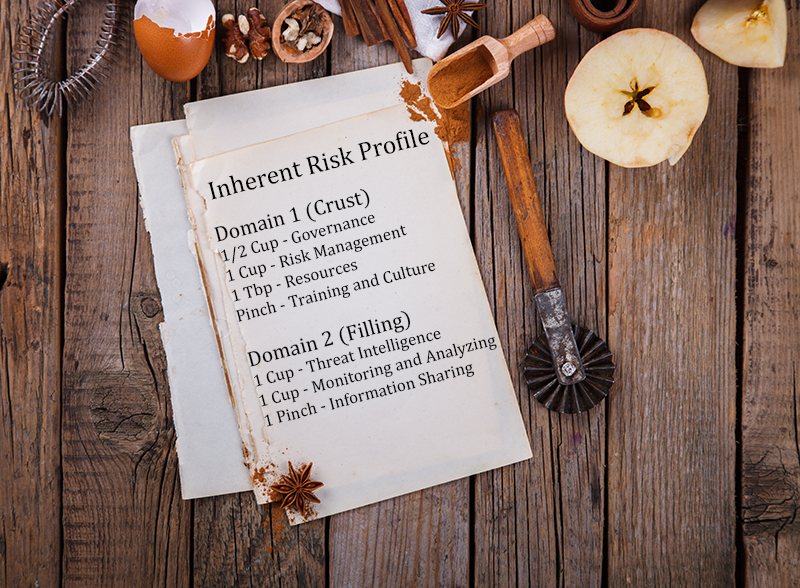
Returning to the pie analogy, the Inherent Risk Profile tells you how much (risk) of each ingredient (maturity domain) is required to make the best pie (ACET-based cybersecurity assessment) for your CU. It should be noted that the Inherent Risk Profile recipe and Cybersecurity Maturity ingredients will differ from CU to CU just like a pie will taste different from region to region based on available ingredients and kitchen available.
If your CU needs help better understanding the recepie or ingredients for a successful ACET pie, Lares would be happy to help. Please contact us today and we’ll make sure that your cybersecurity program is the best program for your CU, your employees, and your members.

Andrew Hay is the COO at Lares and is a veteran cybersecurity executive, strategist, industry analyst, data scientist, threat and vulnerability researcher, and international public speaker with close to 25 years of cybersecurity experience across multiple domains. He prides himself on his ability to execute the security strategy of the company with which he works without neglecting business objectives and the needs of its customers. Andrew is the author of multiple books on advanced security topics and is frequently approached to provide expert commentary on industry developments. He has been featured in publications such as Forbes, Bloomberg, Wired, USA Today, and CSO Magazine.