Tell us a little about yourself.
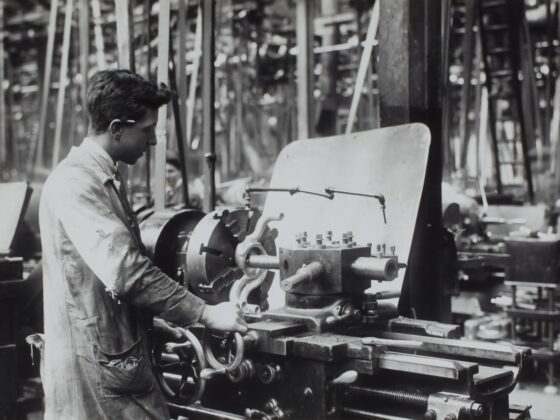
I’ve been active in the community and scene for over a decade now. I joined the Lares application security team back in 2016. Outside of work I enjoy combat robotics because it allows me to combine my electrical engineering and machining talents, and I’m also an avid outdoorsman.
What brought you to Lares?
I had worked at a couple of large consultancies and decided that I wanted to get back into working for a more boutique firm again since they are better places to work and enable me to provide better results to my clients.
What keeps you at Lares?
I really enjoy the people on our team, and they’re absolutely great to work with. We also get a good variety of projects to work on, so it doesn’t feel like I’m testing the same kind of application week after week.
What is your primary focus area?
During work hours, I focus mainly on web application security, process control networks, and cloud implementation security. Outside of work I’ve been working with software-defined radios (SDRs) and robotics a lot lately.
When testing, what is your “go-to” technique?
For the last couple of years, I’ve seen great results from both server-side request forgery (SSRF) and DLL hijacking.
Can you recall a recent defensive tactic that successfully blocked your attempts to gain access?
I’m someone who really believes in having solid fundamentals. An application that’s is written by a team who understands attacker’s methodologies, how to prevent exploitation, and how to put countermeasures in place to limit impact when an exploit is successful is always going to be more secure than an application that is full of holes and has a vendor product bolted on after development.
What’s your favorite security tool and why?
I spend a lot of time in BURP Suite and have really come to appreciate it’s workflow compared to other proxies. When it comes to things that I use less often, I have a Portapack-ed HackRF with the Havoc firmware on it (with a couple of modifications) and I’m constantly amazed at how easy that makes working in the RF space.

Chris Lytle
Sr. Adversarial Engineer
At Lares since 2016
12 years of experience
Areas of expertise include Application Security, SCADA, ICS, and Hardware

Andrew Hay is the COO at Lares and is a veteran cybersecurity executive, strategist, industry analyst, data scientist, threat and vulnerability researcher, and international public speaker with close to 25 years of cybersecurity experience across multiple domains. He prides himself on his ability to execute the security strategy of the company with which he works without neglecting business objectives and the needs of its customers. Andrew is the author of multiple books on advanced security topics and is frequently approached to provide expert commentary on industry developments. He has been featured in publications such as Forbes, Bloomberg, Wired, USA Today, and CSO Magazine.