Overview
R.J. McDown (@BeetleChunks) of the Lares® Research and Development Team discovered a Critical Remote Code Execution vulnerability in the latest version of Microsoft Outlook. R.J. and the Lares R&D team immediately submitted a report to Microsoft detailing this issue. The vulnerability, now designated CVE-2019-1199, was validated against Microsoft Outlook Slow Ring Build Version 1902 (OS Build 11328.20146) running on Windows 10 Enterprise Version 1809 (OS Build 17763.379).
The vulnerability was discovered using a custom fuzzer that was created to target specific segments of an email message with malformed compressed RTF data. After a few iterations, team members noted several crashes resulting from the mishandling of objects in memory. After conducting root cause analysis, it was verified that these crashes were the result of a Use-After-Free condition. Triggering the vulnerability required very little user interaction, as simply navigating out of the Outlook preview pane was enough to trigger the bug, causing Outlook to immediately crash. The following GIF depicts the bug being successfully triggered.
Discovery
One of the message formats supported by Outlook is the .MSG format which conforms to the Microsoft Object Linking and Embedding (OLE) Data Structures standard format (https://docs.microsoft.com/en-us/openspecs/windows_protocols/ms-oleds/85583d21-c1cf-4afe-a35f-d6701c5fbb6f). The OLE structure is similar to a FAT filesystem and can be easily explored with OffVis.
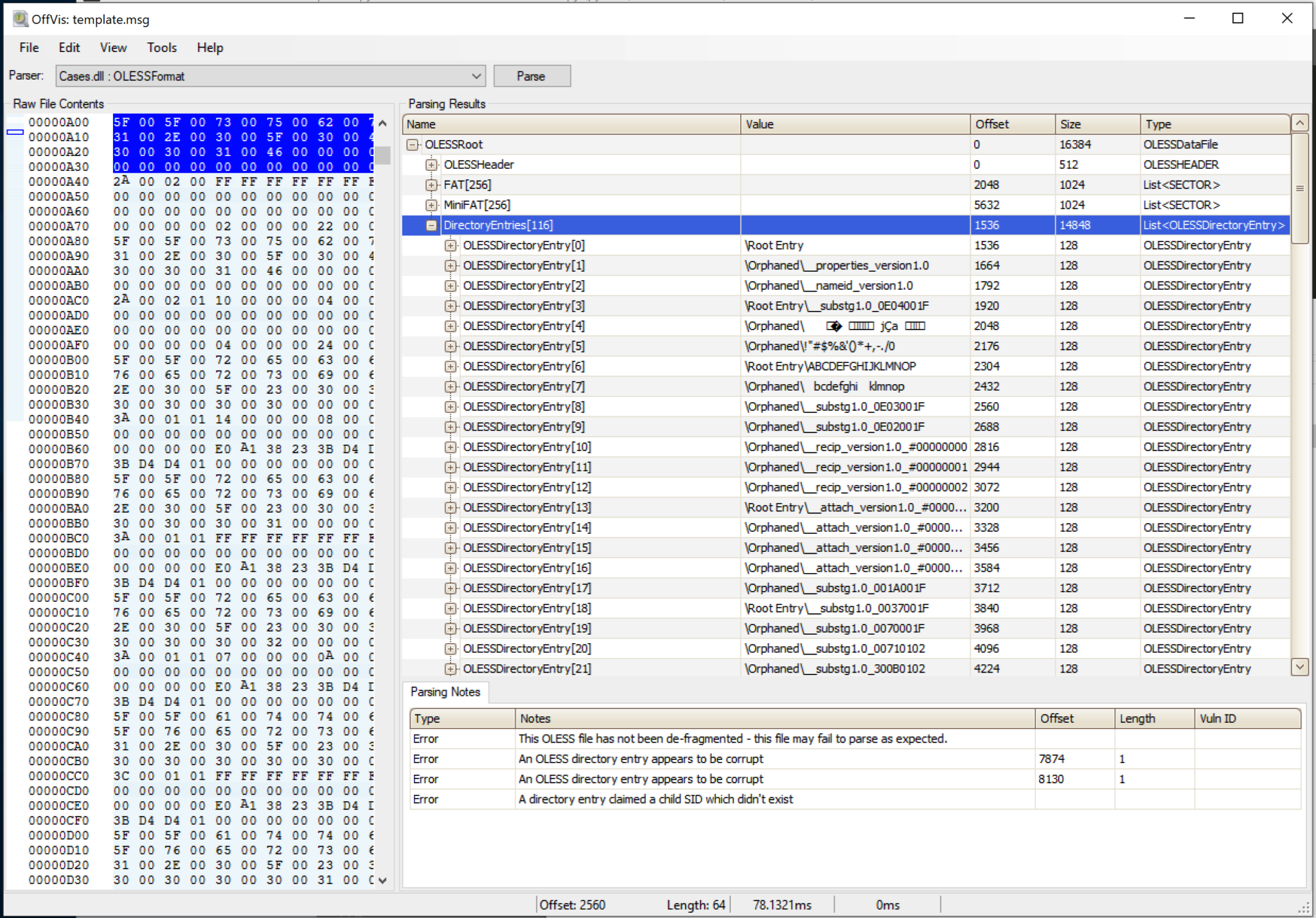
After exploring the MSG format and examining the MS-OLEDS documentation, several structures within the file format were identified as good candidates for fuzzing. Test cases were generated using a Python script that leveraged the OLEFILE library to read a template MSG file, extracted specific properties, ran the data through a custom Radamsa Python wrapper, and then wrote the fuzzed test case to disk. The following code snippet shows the function (fuzz_message_part) that was responsible for the creation of each test case.
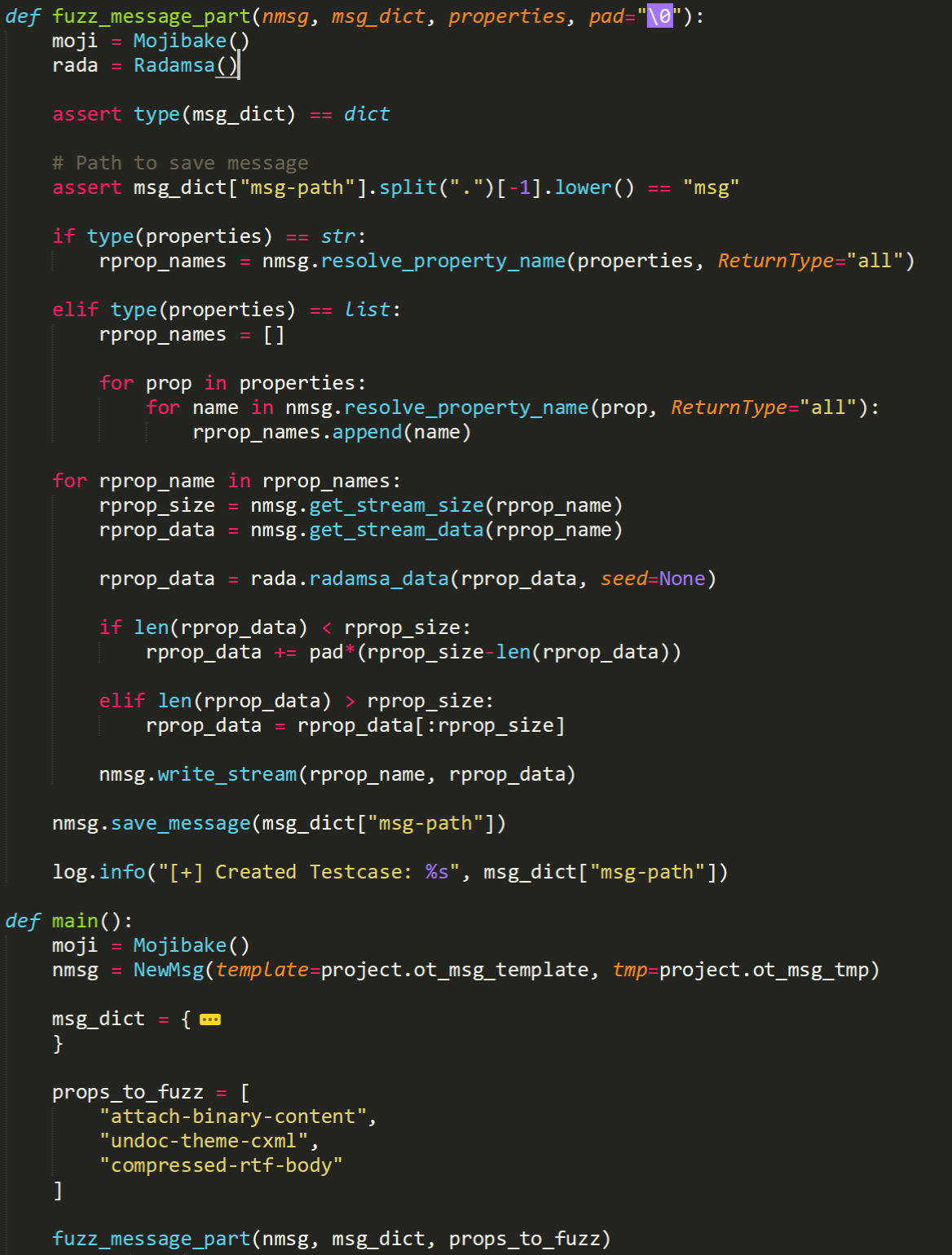
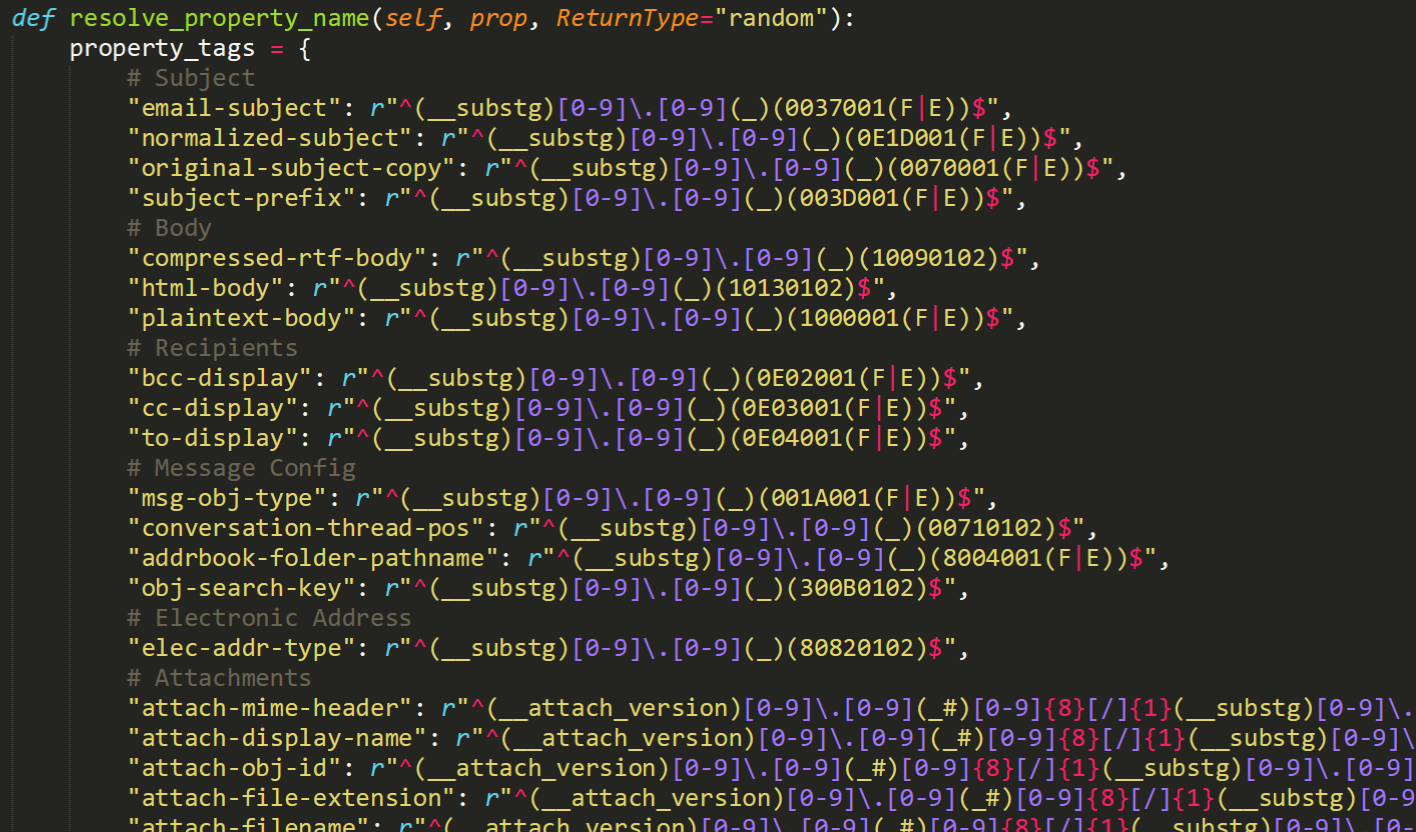
The above code snippet provides a list of message properties in “props_to_fuzz” that are then passed to the “fuzz_message_part()” function. In that function the properties are resolved to locations in the MSG template. The data is then extracted from those locations and run through Radamsa to create a new testcase. The “resolve_property_name()” function simply correlates a property type to a regular expression that will match on the target property. This is shown in the following code snippet.
Although Radamsa is a testcase generator in and of itself, using a more targeted fuzzing method, in our experience, has reduced yield time to results.
The testcase generator was then integrated into SkyLined’s amazing BugID, and a custom notification system was created that reported all new crash data and classification to the team’s Slack channel. After creation of the fuzzing framework was completed, the team noticed crashes occurring after only a few iterations.
Root Cause Analysis
After a few interesting crashes were observed, team members used WinDbg as the primary debugger to begin conducting root cause analysis. WinDbg was attached to Outlook, and the test case was opened in Outlook resulting in an immediate access violation.
After selecting the test case, the Outlook Preview Pane invoked parsing of the message body resulting in the following exception (Image Base: 7ff7c0d00000):
outlook!StdCoCreateInstance+0x82c0: 7ff7c0e3c100 -> 7ff7c0e3cc24 outlook+0x80850: 7ff7c0d80850 -> 7ff7c0d80e85 outlook+0x81ce0: 7ff7c0d81ce0 -> 7ff7c139a2ab outlook!HrShowPubCalWizard+0x101b0c: 7ff7c1afe05c -> 7ff7c1afe0d1 outlook!HrShowPubCalWizard+0x101198: 7ff7c1afd6e8 -> 7ff7c1afd7af outlook!FOutlookIsBooting+0x4620: 7ff7c0e41920 -> 7ff7c0e41b04 outlook!FOutlookIsResuming+0x38200: 7ff7c1021f00 -> 7ff7c1021f68 outlook!FOutlookIsResuming+0x1f6a0: 7ff7c10093a0 -> 7ff7c100942c outlook+0xafb04: 7ff7c0dafb04 -> 7ff7c0dafb16 outlook!HrGetOABURL+0x77938: 7ff7c1110598 -> 7ff7c1110613 VCRUNTIME140!_CxxThrowException
Next, a breakpoint was set on “outlook!StdCoCreateInstance+0x82c0: 7ff7c0e3c100” and execution of was Outlook was continued. While Outlook was running, another component within Outlook GUI, such as an email message, folder, button, etc. was selected. After doing so, another application exception occurred while attempting to execute an address that referenced unmapped memory.
outlook!StdCoCreateInstance+0x82c0:
7ff7c0e3c100
outlook+0x80850:
7ff7c0d80850
outlook+0x81ce0:
7ff7c0d81ce0
outlook+0x7419e:
7ff7c0d7419e -> crash occurs (test byte ptr [rcx],1 ds:0000020b`00a76ffc=??)
WinDbg’s heap function was used to analyze the address pointed to by the instruction pointer at the time of the second exception. This showed that the application crashed while attempting to reference data in a heap block that was in a freed state. Further analysis was conducted, however this confirmed the presence of a Use After Free (UAF) condition.
0:000> !heap -p -a 20b00a76ffc
address 0000020b00a76ffc found in
_DPH_HEAP_ROOT @ 20b17571000
in free-ed allocation ( DPH_HEAP_BLOCK: VirtAddr VirtSize)
20b0003c820: 20b00a76000 2000
00007ff9e51b7608 ntdll!RtlDebugFreeHeap+0x000000000000003c
00007ff9e515dd5e ntdll!RtlpFreeHeap+0x000000000009975e
00007ff9e50c286e ntdll!RtlFreeHeap+0x00000000000003ee
00007ff9ad247f23 mso20win32client!Ordinal668+0x0000000000000363
00007ff9ad1a2905 mso20win32client!Ordinal1110+0x0000000000000065
00007ff7c0d74a55 outlook+0x0000000000074a55
00007ff7c0d7449f outlook+0x000000000007449f
00007ff7c0dbe227 outlook+0x00000000000be227
00007ff7c0dbcdaf outlook+0x00000000000bcdaf
00007ff7c0dbb9e0 outlook+0x00000000000bb9e0
00007ff7c12db320 outlook!HrGetCacheSetupProgressObject+0x0000000000008740
00007ff7c0da75e7 outlook+0x00000000000a75e7
00007ff7c0da7373 outlook+0x00000000000a7373
00007ff7c0eaae24 outlook!RefreshOutlookETWLoggingState+0x0000000000023694
00007ff7c0eaa525 outlook!RefreshOutlookETWLoggingState+0x0000000000022d95
00007ff7c0d6d946 outlook+0x000000000006d946
00007ff7c0d6d2d4 outlook+0x000000000006d2d4
00007ff9e2d5ca66 USER32!UserCallWinProcCheckWow+0x0000000000000266
00007ff9e2d5c34b USER32!CallWindowProcW+0x000000000000008b
00007ff9d55ab0da Comctl32!CallNextSubclassProc+0x000000000000009a
00007ff9d55aade8 Comctl32!TTSubclassProc+0x00000000000000b8
00007ff9d55ab0da Comctl32!CallNextSubclassProc+0x000000000000009a
00007ff9d55aaef2 Comctl32!MasterSubclassProc+0x00000000000000a2
00007ff9e2d5ca66 USER32!UserCallWinProcCheckWow+0x0000000000000266
00007ff9e2d5c582 USER32!DispatchMessageWorker+0x00000000000001b2
00007ff7c0dd9a10 outlook+0x00000000000d9a10
00007ff7c1051b85 outlook!IsOutlookOutsideWinMain+0x0000000000005545
00007ff7c0f104e7 outlook!HrBgScheduleRepairApp+0x000000000004a4d7
00007ff7c105b646 outlook!OlkGetResourceHandle+0x00000000000045d6
00007ff9e4b981f4 KERNEL32!BaseThreadInitThunk+0x0000000000000014
00007ff9e511a251 ntdll!RtlUserThreadStart+0x0000000000000021
Conclusion
Exploitation of the vulnerability requires that a user open a specially crafted file with an affected version of Microsoft Outlook software. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file. In a web-based attack scenario, an attacker could host a website (or leverage a compromised website that accepts or hosts user-provided content) that contains a specially crafted file designed to exploit the vulnerability. An attacker would have no way to force users to visit the website. Instead, an attacker would have to convince users to click a link, typically by way of an enticement in an email or instant message, and then convince them to open the specially crafted file.
At the time of this publication, Microsoft has not identified any mitigating factors or workarounds for this vulnerability. The only way to fix this issue is to apply the August 2019 Security Update.
We encourage you to monitor the Microsoft advisory for any updates: https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2019-1199.
If your organization would like to confirm if this issue affects your deployed systems, or to ensure that the patch was properly applied, please do not hesitate to contact us at sales@lares.com. We’d be happy to arrange a time to validate our findings within your organization.

Andrew Hay is the COO at Lares and is a veteran cybersecurity executive, strategist, industry analyst, data scientist, threat and vulnerability researcher, and international public speaker with close to 25 years of cybersecurity experience across multiple domains. He prides himself on his ability to execute the security strategy of the company with which he works without neglecting business objectives and the needs of its customers. Andrew is the author of multiple books on advanced security topics and is frequently approached to provide expert commentary on industry developments. He has been featured in publications such as Forbes, Bloomberg, Wired, USA Today, and CSO Magazine.